Microsoft Security Baseline Understanding
Note: History of changes to this blog post can be found at the bottom
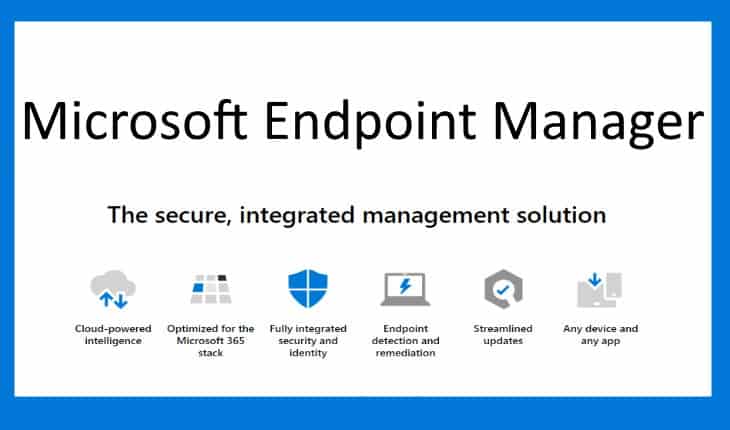
Microsoft has been hard at work consolidating their security messaging and in the past 6- 12 months there has been a number of changes to their security products which has caused some confusion to customers and partners. In this blog I am attempting to explain (mostly to myself – but I hope others benefit as well) the current state of the Microsoft Security solution offerings.
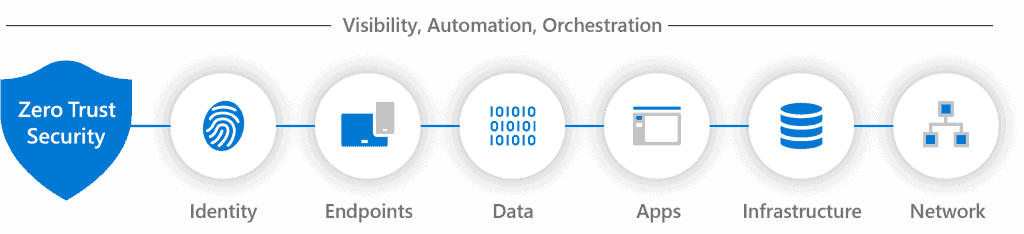
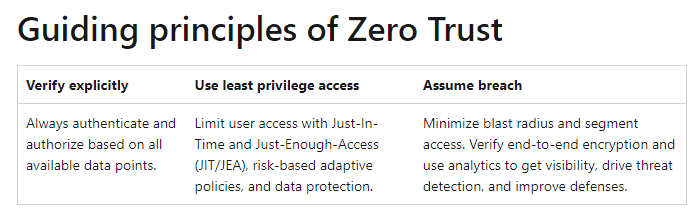
Earlier this year I created a quick 15 minute video (and associated blog post) called Cybersecurity Fundamentals, in which I explained some of the basics and provided a baseline overview of the why, what and how cybersecurity best practices are so important to implement. The very first thing we should note is that Microsoft is a huge proponent of Zero Trust security concepts and strategy ( see blog.)
It has been very interesting to watch the pace of change and reorganization of product lines. Essentially, I think all of these products have existed in their own spaces independent from each other, but now ( finally) they are all part of of one cohesive and comprehensive initiative that makes sense. For a while now, Microsoft has had a program called Microsoft Security Service Provider (MSSP) in which authorized partners can be assigned by customers to manage and support customer’s security via Azure Lighthouse portal. The latest development in the journey — as of this writing — happened in early May 2022 when program and the Microsoft Security Experts effort within it.
Microsoft is taking a very agnostic point of view to security, which is to say that they can extend their security monitoring and response to any device or application or service no matter what cloud it resides on. This is very good news for most in the industry. The sheer amount of security related signals collected and monitor by Microsoft on their customer base are staggering and they are putting it to use to fight against bad actors.
There are 4 product families ( Defender, Entra, Purview and Priva) within the Microsoft Security area. In addition, there are a couple of overarching services not defined within these families that stand on their own:
- Microsoft Secure Score is a measurement of an organization’s security posture, with a higher number indicating more improvement actions taken.
- Microsoft Sentinel is a scalable, cloud-native, security information and event management (SIEM) and security orchestration, automation, and response (SOAR) solution. Microsoft Sentinel delivers intelligent security analytics and threat intelligence across the enterprise, providing a single solution for attack detection, threat visibility, proactive hunting, and threat response.
Below is what I understand each to be as of this writing:
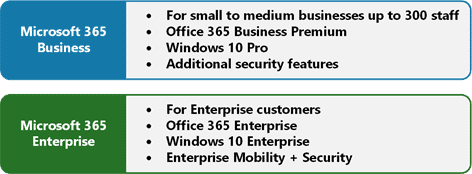
Enterprise Mobility + Security
Enterprise Mobility + Security is Microsoft’s offering that provides an agile, comprehensive set of mobility and security solutions enabling a pathway to mobility and the cloud. Microsoft’s EMS has four main components: Azure Active Directory Premium, Microsoft Intune, Azure Rights Management, and Microsoft Advanced Threat Analytics.
It is offered in two version E3 & E5. Capabilities included are:
Enterprise Mobility + Security E3 includes
- Azure Active Directory Premium P1
- Microsoft Intune
- Azure Information Protection P1
- Microsoft Advanced Threat Analytics
- Azure Rights Management (part of Azure Information Protection)
- Windows Server CAL rights
Enterprise Mobility + Security E5 includes:
All features of Enterprise Mobility + Security E3 plus
- Azure Active Directory Premium (AADP) P2
- Azure Information Protection P2
- Microsoft Cloud App Security
- Azure Active Directory [AD] Identity Protection (as a feature of AADP P2)
- Azure Advanced Threat Protection
- Azure AD Privileged Identity Management (as a feature of AADP P2)
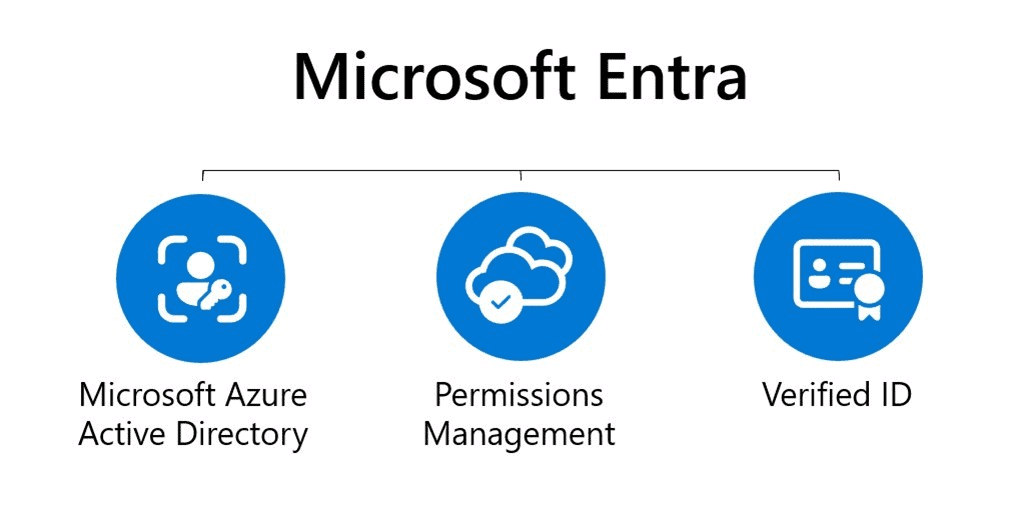
Identity & Access Products – Microsoft Entra
Microsoft Entra product family is an integrated solution that protects each identity and secures every access point in our hyperconnected world. It helps protect your organization by securing access to the connected world for all of your users, smart devices, and services. It includes new and existing tools such as Azure Active Directory (Azure AD), Cloud Infrastructure Entitlement Management (CIEM), and Decentralized Identity.
| Product | Brief Description | License |
|---|---|---|
| Azure Active Directory | A solid security strategy, begins with a secure user identity and manage the access it provides. Azure Active Directory, a comprehensive and complete identity and access management solution. Azure Active Directory comes in four editions—Free, Office 365 apps, Premium P1, and Premium P2. See my blog post on this here | |
| Microsoft Entra Permissions Management | Discover, remediate, and monitor permission risks across your multicloud infrastructure with a cloud infrastructure entitlement management (CIEM) solution. | |
| Microsoft Entra Verified ID | Create, issue, and verify privacy-respecting decentralized identity credentials with an identity verification solution that helps you enable more secure interactions with anyone or anything. |
Thread Detection & Protection – Microsoft Defender
The Microsoft Defender family offers comprehensive threat prevention, detection, and response capabilities for everyone—from individuals looking to protect their family to the world’s largest enterprises. Defend against modern attacks with cloud-native SIEM and XDR
| Product | Brief Description | . |
|---|---|---|
| Microsoft 365 Defender | Microsoft 365 Defender is a unified pre- and post-breach enterprise defense suite that natively coordinates detection, prevention, investigation, and response across endpoints, identities, email, and applications to provide integrated protection against sophisticated attacks. | |
| Microsoft Defender for Identity | Microsoft Defender for Identity (formerly Azure Advanced Threat Protection, also known as Azure ATP) is a cloud-based security solution that leverages your on-premises Active Directory signals to identify, detect, and investigate advanced threats, compromised identities, and malicious insider actions directed at your organization. | |
| Microsoft Defender for Endpoint | Discover and defend Windows, macOS, Linux, Android, iOS, and network devices against sophisticated threats. Microsoft Defender for Endpoint coordinates prevention, detection, and response to provide comprehensive protection against sophisticated cyberattacks. | |
| Microsoft Defender for Office 365 | Microsoft Defender for Office 365 is a cloud-based email filtering service that helps protect your organization against advanced threats to email and collaboration tools, like phishing, business email compromise, and malware attacks. Defender for Office 365 also provides investigation, hunting, and remediation capabilities to help security teams efficiently identify, prioritize, investigate, and respond to threats. Microsoft Defender for Office 365 safeguards your organization against malicious threats posed by email messages, links (URLs), and collaboration tools. Defender for Office 365 includes: Threat protection policies: Define threat-protection policies to set the appropriate level of protection for your organization. Reports: View real-time reports to monitor Defender for Office 365 performance in your organization. Threat investigation and response capabilities: Use leading-edge tools to investigate, understand, simulate, and prevent threats. Automated investigation and response capabilities: Save time and effort investigating and mitigating threats. Microsoft Defender for Office 365 is available in two versions Plan 1 and Plan2 | |
| Microsoft Defender for Cloud | Protect your multi-cloud and hybrid cloud workloads with built-in extended detection and response (XDR ) capabilities | |
| Microsoft Sentinel | Microsoft Sentinel is a scalable, cloud-native, security information and event management (SIEM) and security orchestration, automation, and response (SOAR) solution. Microsoft Sentinel delivers intelligent security analytics and threat intelligence across the enterprise, providing a single solution for attack detection, threat visibility, proactive hunting, and threat response. | |
| Microsoft Defender for Cloud Apps | Get deep visibility and control of cloud apps with a leading cloud access security broker. | |
| Microsoft Defender for IoT | Get full visibility and continuous threat monitoring of your IoT infrastructure. |
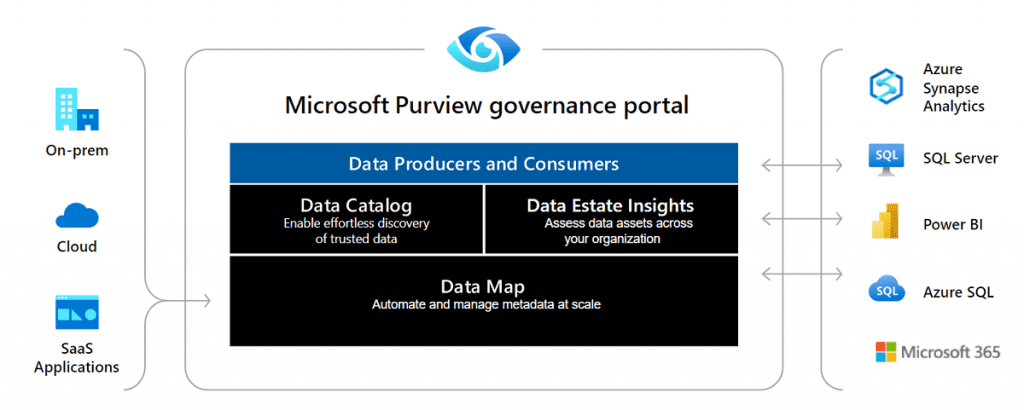
Information protection and governance – Microsoft Purview
Microsoft Purview family provides a unified data governance solution to help manage and govern your on-premises, multi-cloud, and software as a service (SaaS) data. Easily create a holistic, up-to-date map of your data landscape with automated data discovery, sensitive data classification, and end-to-end data lineage. Enable data consumers to access valuable, trustworthy data management.
| Product | Brief Description | License |
|---|---|---|
| Microsoft Purview Information Protection | Implement Information Protection to help you discover, classify, and protect sensitive information wherever it lives or travels. | |
| Microsoft Purview Data Lifecycle Management | Use Purview Data Lifecycle Management capabilities to govern your data for compliance or regulatory requirements. | |
| Microsoft Purview Data Loss Prevention | Apply a consistent set of policies across the cloud, on-premises environments, and endpoints to monitor, prevent, and remediate risky activities with sensitive data. | |
| Microsoft Purview Communication Compliance | Quickly identify and remediate code of conduct policy violations that occur across company communications. Support a healthy work environment and meet industry-specific compliance requirements | |
| Microsoft Purview eDiscovery | Use machine learning capabilities—such as near-duplicate detection, email threading, relevance, themes, and smart tags—to help customers reduce and cull large volumes of data. It is available in two flavors: eDiscovery Standard & eDiscovery Premium | |
| Microsoft Purview Advanced Message Encryption | Microsoft Purview Advanced Message Encryption is included in Microsoft 365 Enterprise E5. It helps customers meet compliance obligations that require more flexible controls over external recipients and their access to encrypted emails. You can control sensitive emails shared outside the organization with automatic policies and track those activities through the encrypted message portal access logs. | |
| Microsoft Purview Customer Lockbox | Customer Lockbox ensures that Microsoft can’t access your content to do service operations without your explicit approval. Customer Lockbox brings you into the approval workflow process that Microsoft uses to ensure only authorized requests allow access to your content. |
Privacy Management – Microsoft Priva
A privacy management solution that proactively identifies and helps protect against privacy risks, empower employees to make smart data handling decisions, and automate and manage subject requests at scale
| Product | Brief Description | License |
|---|---|---|
| Microsoft Priva Risk Management | . Microsoft Priva is a new category of features in Microsoft Compliance Centre, providing solutions targeted at Data privacy compliance. It gives you the capability to set up policies that identify privacy risks in your Microsoft 365 environment and enable easy remediation. The Microsoft Priva brand is now available with its first set of Priva solutions: Priva Privacy Risk Management – a sensitive information template based capability to create privacy risk management policies to identify and remediate privacy risks such as data transfers, data overexposure, and data minimization, and empower information workers to make smart data handling decisions. Priva Subject Rights Requests – helps automate and manage data subject access requests process and related case management workflows. |
Other security products not mentioned above include:
| Product | Brief Description | License |
|---|---|---|
| Azure Identity Protection | Azure Identity Protection is a tool that allows organizations to accomplish three key tasks: Automate the detection and remediation of identity-based risks. Investigate risks using data in the portal. Export risk detection data to your SIEM. Identity Protection uses the learnings Microsoft has acquired from their position in organizations with Azure AD, the consumer space with Microsoft Accounts, and in gaming with Xbox to protect your users. Microsoft analyses 6.5 trillion signals per day to identify and protect customers from threats. The signals generated by and fed to Identity Protection, can be further fed into tools like Conditional Access to make access decisions, or fed back to a security information and event management (SIEM) tool for further investigation based on your organization’s enforced policies. | |
| Azure AD Privileged Identity Management | Privileged Identity Management (PIM) is a service in Azure Active Directory (Azure AD) that enables you to manage, control, and monitor access to important resources in your organization. These resources include resources in Azure AD, Azure, and other Microsoft Online Services such as Microsoft 365 or Microsoft Intune. The following video introduces you to important PIM concepts and features. | |
| Azure AD External Identities | Azure AD External Identities refers to all the ways you can securely interact with users outside of your organization. If you want to collaborate with partners, distributors, suppliers, or vendors, you can share your resources and define how your internal users can access external organizations. If you’re a developer creating consumer-facing apps, you can manage your customers’ identity experiences. Capabilities that make up external identities include: B2B collaboration , B2B direct connect and Azure AD B2C. | |
| Microsoft Identity Manage (MIM) | Microsoft Identity Manager (MIM) 2016 extends the reach of Azure Active Directory, Microsoft’s identity and access management solution. MIM ensures consistent user identities by seamlessly bridging multiple on-premises authoritative systems and authentication stores like Active Directory, SAP, Oracle, and other LDAP and SQL systems. When used with Active Directory, Azure AD Connect and Azure Active Directory, this solution provides consistent experiences for signing into on-premises and SaaS applications. | |
| Exchange Online Protection | Exchange Online Protection (EOP) is the cloud-based filtering service that protects your organization against spam, malware, and other email threats. EOP is included in all Microsoft 365 organizations with Exchange Online mailboxes. |
Updates (Change log) to this blog article below
7/11/2022:
Added Microsoft Mobility + Security (EMS) section
Added Azure Active Directory Free, Premium 1 and Premium 2 references
Added Other Security Products Section
Added to Microsoft Defender section:
- Microsoft Defender for Identity row
Added to Microsoft Purview eDiscovery section:
- eDiscovery Standard and eDiscovery Premium references
- Microsoft Purview Advanced Message Encryption
Additional Resources:
- IT Security Modernization with Microsoft 365 – Modern EUC Blog – came across this video from a competitor brand that explains in great detail why is Microsoft 365 vital for IT Security Modernization….
- Chief Information Security Officer (CISO) Workshop – Security documentation | Microsoft Docs
- Microsoft Security Blog – Digital Security Tips and Solutions
- Zero Trust implementation guidance | Microsoft Docs – Zero Trust is a security strategy and an approach in designing and implementing the set of security principles (Verify explicitly, Use least privilege access & Assume breach)